The boring layer that keeps the agentic layer auditable.
Same discipline we apply to our own production stack. Two engagements in this column: production-server hardening on Linux and Windows, and the secure-AI-routing bridge that lets your engineers use agentic CLIs without your data leaving the building through a vendor's public endpoint.
CIS-benchmark hardening for production servers. As a sprint, or under a small monthly retainer.
OS hardening to the relevant CIS Benchmark — Ubuntu LTS, RHEL, Debian on the Linux side; Windows Server 2019 and 2022 on the Microsoft side. Service-account hygiene, sudoers / RBAC review, SSH and RDP lockdown, host firewall posture, AV/EDR alignment.
Monthly patch windows. Security-advisory triage between windows. Kernel, runtime and dependency updates rolled with a backup before, a smoke test after, and a documented rollback path. Nothing applied silently to anything you depend on for revenue.
syslog and Windows Event Log forwarding to your SIEM (or one we stand up). Authentication-event coverage on both sides. Retention by class — security events held longer than housekeeping noise. Auditable from a workstation, not just from the SIEM console.
Directory-joined where it makes sense, local-with-discipline where it doesn't. Network segmentation at the host firewall and at the cloud subnet. Least privilege by default; admin paths fenced and logged; emergency-break-glass documented.
A single hardening sprint — typically two weeks per ten or so hosts, with a written report and a remediation log. Or a small retainer — monthly patch window plus a quarterly review against drift. We will tell you which fits during the diagnostic.

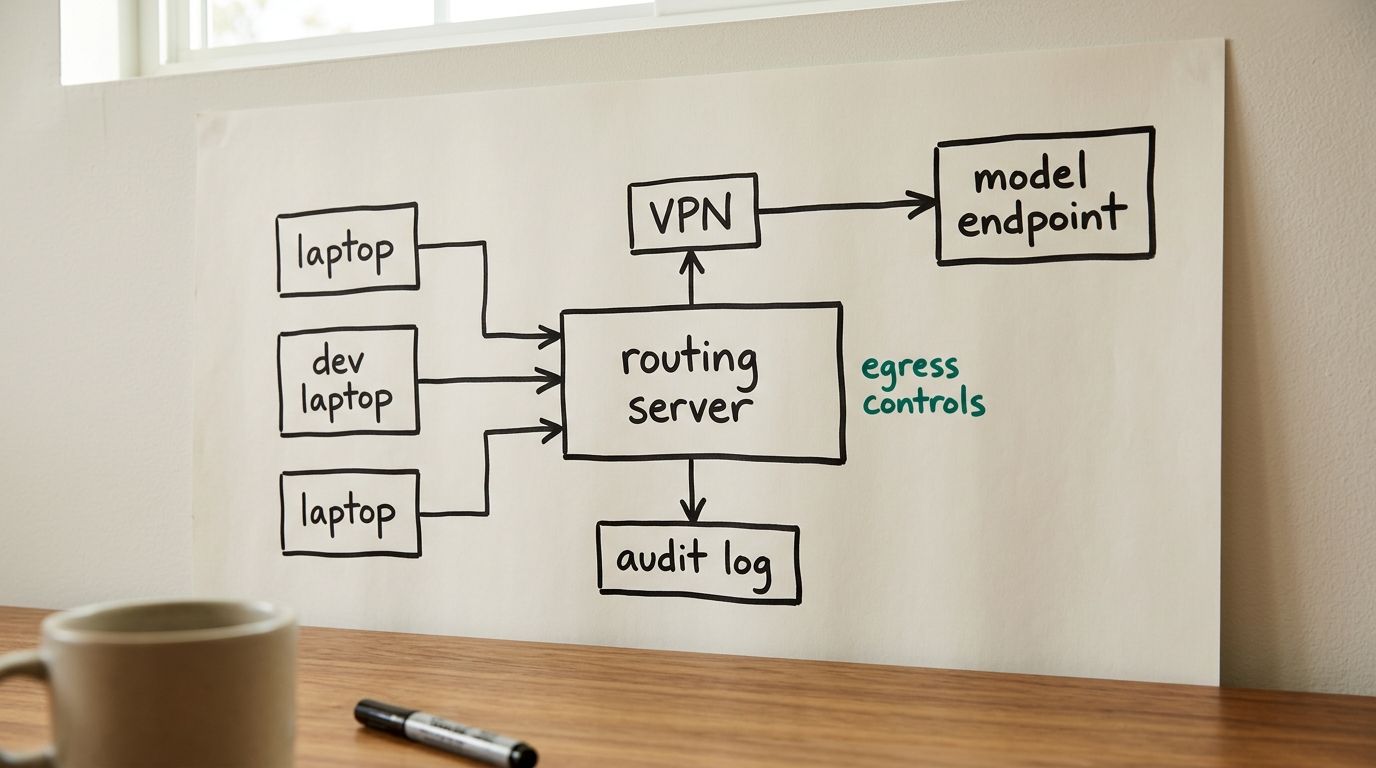
Route agentic CLI sessions and API calls through your own perimeter — server, VPN, egress controls, audit log.
- The problem. Your engineers want Claude Code, Codex CLI, Gemini CLI. Your data classification doesn't allow code or context to leave the building through a vendor's public endpoint without controls. The fix is not "ban the tools" — it's plumbing that you operate.
- What we ship. A routing server you operate, sitting between developer machines and the model vendor. VPN-fronted, egress-controlled, with full request and response audit logging. Approved tools, approved domains, approved working hours — the policy is yours, the enforcement is on the wire.
- What it preserves. The developer experience of Claude Code, Codex CLI and Gemini CLI as your engineers already know them. No bespoke wrapper, no second IDE, no context-window shrinkage by middleware.
- What it does not claim. It is not an LLM running in your VPC, and it is not a guarantee of model-side data handling. It is the perimeter, the plumbing and the audit trail you need to use vendor models responsibly under PDPA-class data controls.
- Engagement shape. A two-to-four-week setup, with a runbook and a small operations retainer for the first quarter. After that, your team operates it; we are on call.
The diagnostic week is paid up front and produces a written scoping report — host inventory and remediation backlog for hardening, network and policy diagram for routing. You keep the report whether or not we run the engagement.
Brief us →